Move supplier assurance off spreadsheets.
Map your suppliers, automate evidence collection and give your board an audit-ready view of NIS2 risk — without staffing a security team. Built on Microsoft 365, hosted in the EU.
Three jobs, one product.
Continuously assess every supplier against NIS2 controls. The risk questionnaire produces a structured tier — by worst dimension — so you can spot the supplier that puts you in scope of a fine before the auditor does.
Collect a supplier’s evidence once and reuse it across every assurance request. The library finds prior uploads automatically — no re-keying the same answers across customer spreadsheets.
One-click board packs and regulator-ready bundles. Decision history, evidence pack, posture letter — every approval, rejection and resubmission stamped with actor, rationale and timestamp.
From spreadsheet chaos to audit-ready, in four steps.
Import your supplier list. Auto-classified by tier and lineage traced where data permits.
Evidence requests sent. Replies tracked, library matches surfaced, and reuse offered.
Risk questionnaire produces a tier "by worst dimension". Posture scored against NIS2 in real time.
Board pack and regulator export — one click. Decision trace exportable for any audit request.
Three screens. Three stories.
Real product, redacted. The numbers and supplier names are placeholders; the product is real.
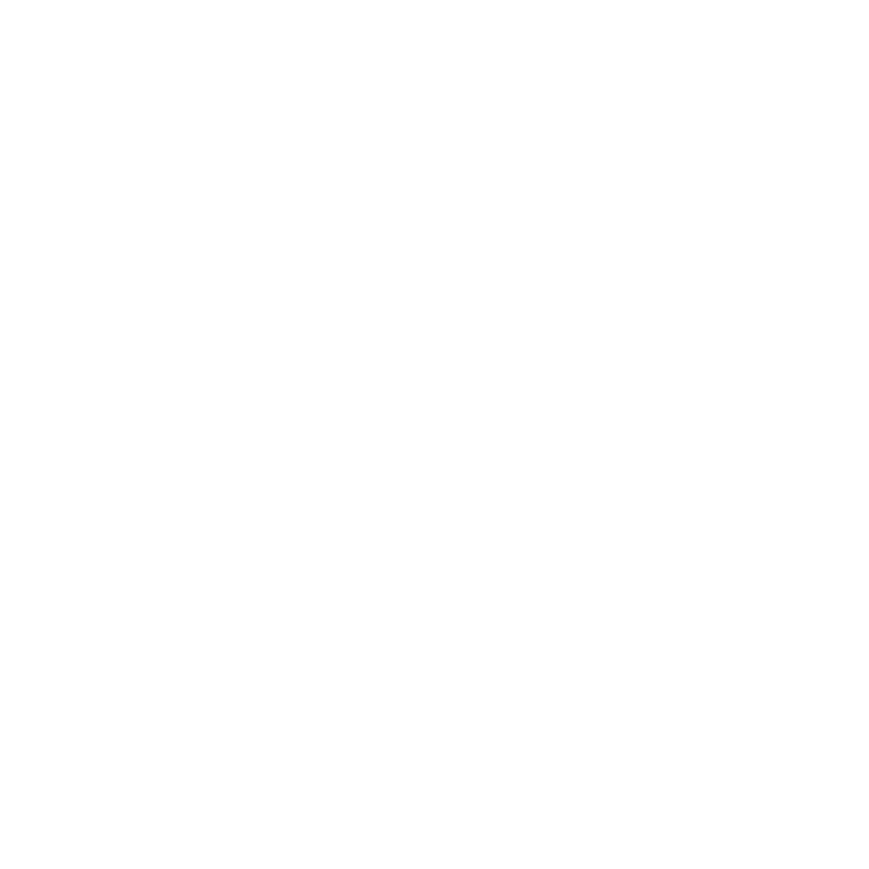
Risk scored by worst dimension.
The questionnaire walks through scope, impact, geography, resilience and assurance. Each answer is colour-coded — Low / Medium / High / Critical — and the supplier’s overall tier is set by their worst dimension, not an average. So one weak answer is never hidden behind nine good ones.
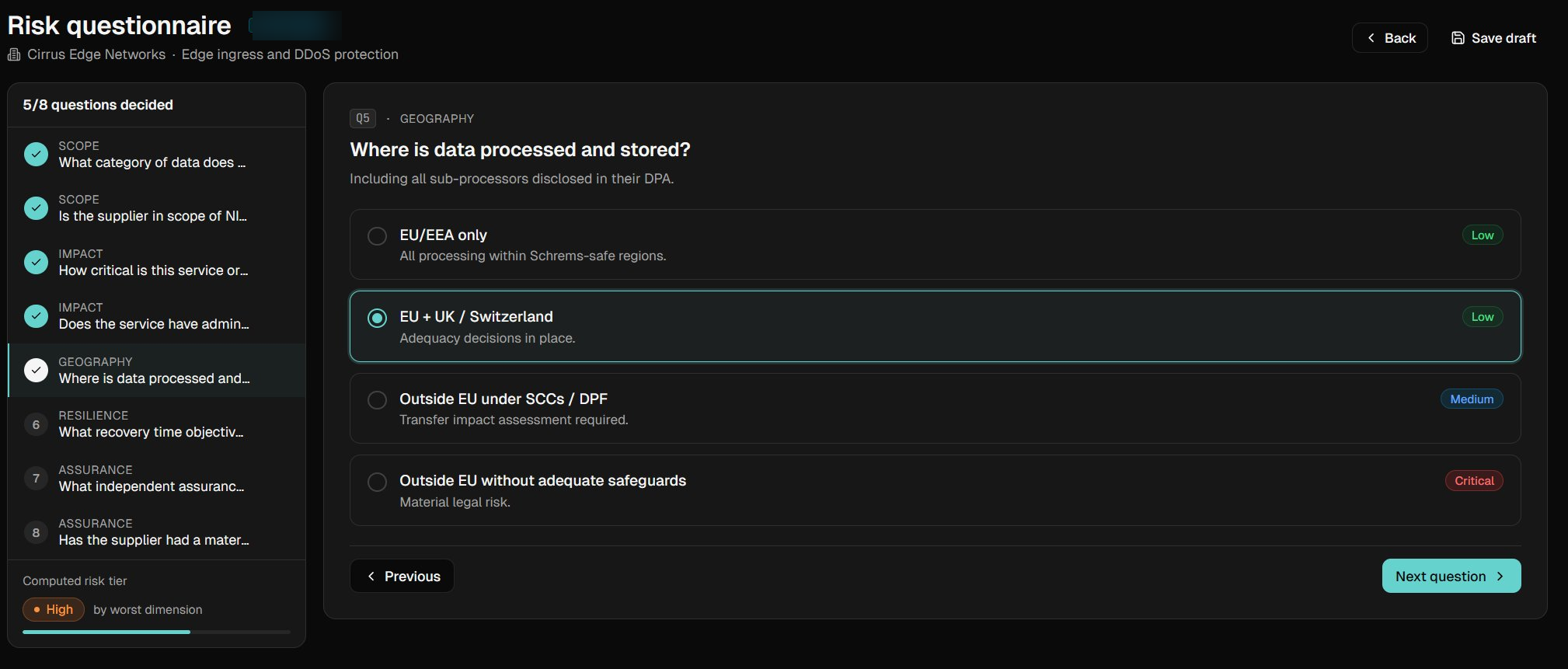
The library pulls prior evidence forward.
When a buyer asks for a sub-processor declaration, the library spots that you uploaded one for a different customer two weeks ago — and offers to reuse it. Re-keying the same answers across customer spreadsheets stops here.
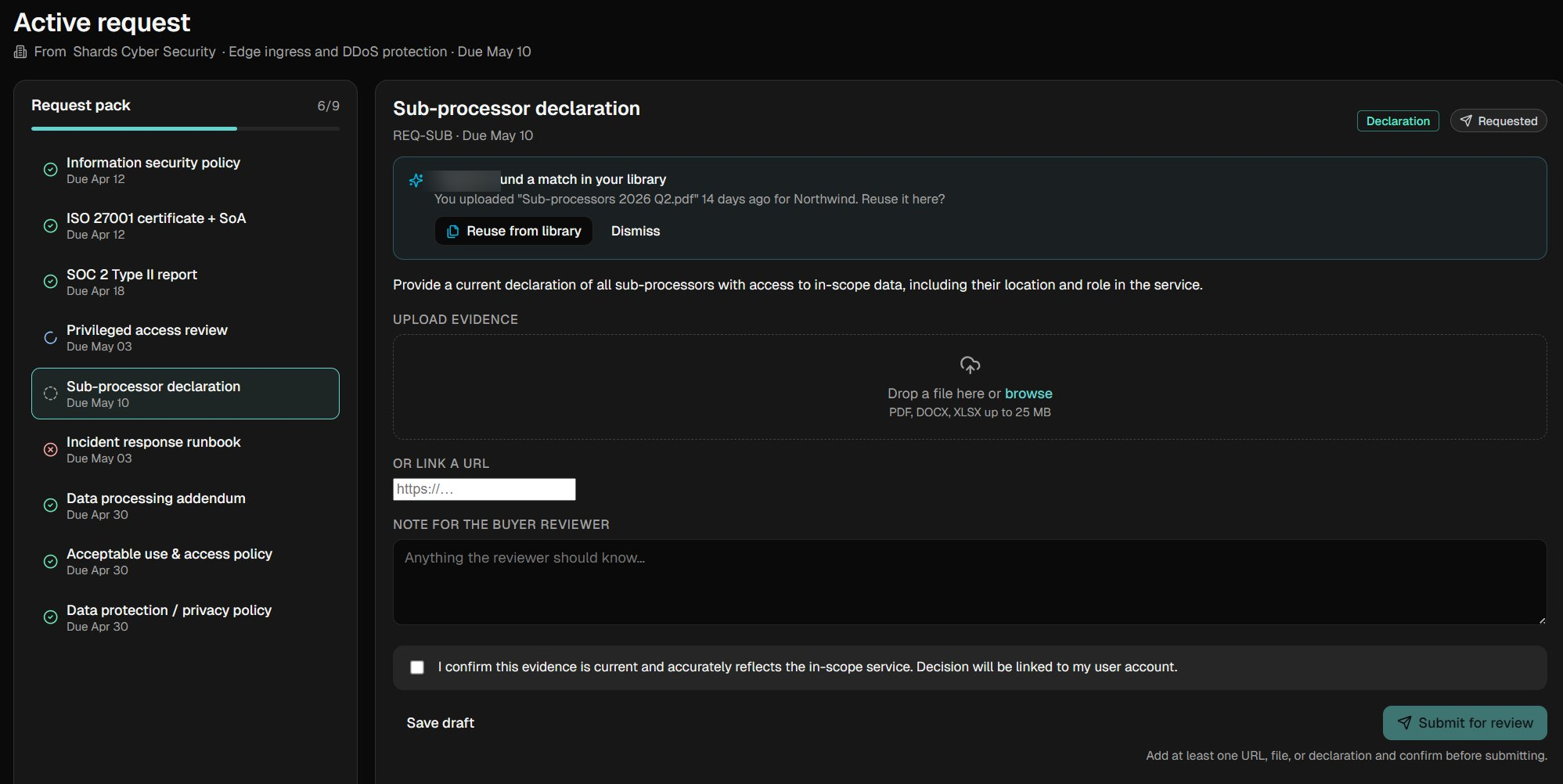
Every decision, stamped and exportable.
Every approval, rejection and resubmission is logged with the actor, the reason and the timestamp. Auditors get a chronological export that closes regulator questions in minutes, not weeks.
If you’re in scope of NIS2, or sell to someone who is.
Energy, transport, banking, financial market infrastructure, healthcare, drinking water, digital infrastructure. Direct NIS2 obligations from October 2024.
Postal, waste, food production and distribution, manufacturing of critical products, digital providers, research. Same controls, same supply-chain scrutiny.
You don’t need to be NIS2-regulated yourself. If you sell to anyone in Annex I or II, your customers are obligated to assess your posture — and increasingly, automate that ask.
We didn't shrink an enterprise tool. We rebuilt the job.
Most assurance tools target enterprise procurement teams. We built ours for the businesses inside the supply chain.
Reuse the evidence you already collected. Stop filling in another vendor questionnaire from scratch every month.
Controls, evidence schemas and exports are all pre-aligned to NIS2. No configuration project required.
The boring stuff done right.
Hosting, integrations, controls and audit-trail — table stakes for any buyer who reads their own DPA.
Connects directly to Defender, Entra ID, Purview and Intune so your existing tenancy is the source of truth — no parallel database to drift.
Data stays inside the EU. Single-tenant and customer-managed encryption available for regulated workloads.
Every approval, rejection and resubmission is logged with the actor, the rationale and the timestamp. Exportable for any auditor request.
Controls, evidence schemas and exports are pre-mapped to NIS2 and ISO 27001 Annex A. No bespoke configuration project to start.
Get a look before general availability.
We’re onboarding a small group of NIS2-scoped SMBs and their key suppliers. Pilot members shape the roadmap and lock in launch pricing.
Request pilot access- White-glove onboarding from the founding team
- Direct line to product for feature requests
- Locked-in pilot pricing through general availability
- Quarterly business review with your account lead
Common questions
Is the product available today?+
Supply Chain Assurance is in private pilot. Join the pilot from the contact form to get access ahead of general availability.
Do I need to be NIS2-regulated to use it?+
No. Many of our pilot customers are suppliers to NIS2-regulated firms and use it to demonstrate posture in assurance requests they receive.
How is data hosted?+
EU-hosted by default in the Slovak Republic / wider EU. Single-tenant deployments available on request.
How is this different from your managed security services?+
Managed Services secure your business. Supply Chain Assurance secures the suppliers your business depends on. The two are complementary — many customers run both.
How does the lineage tracing work?+
Where a supplier discloses its sub-processors and downstream providers, we map the chain and surface the highest-risk path. Most supplier lists only show your direct (Tier 1) relationships; the real risk often hides two or three hops deeper.
How is evidence reused across requests?+
Once a supplier uploads policies, certificates or attestations to their library, future assurance requests pull the existing evidence forward automatically. Re-keying the same answers across spreadsheets stops.
Built by practitioners, not salespeople.
Shards Cybersecurity was founded by Pavel Láska, who spent over a decade in cybersecurity — including nine years on the security team at the Bank of England.
Shards started as a managed security services provider for SMBs. Watching client after client struggle with the same broken supplier-assurance workflow — spreadsheets, emailed PDFs, lost evidence trails — convinced us to build Supply Chain Assurance to solve it properly.
The product itself was shaped by quiet conversations with practising CISOs and security leads across regulated industries — people who've sat in the audit chair, defended supplier decisions to boards, and lived with the consequences. They're not named on this page, but they're in the product.
Bratislava-based. Microsoft Partner. NIS2 specialists.
Ready to see it on your data?
Book a 30-minute demo and we'll show you what your supply chain posture looks like today.